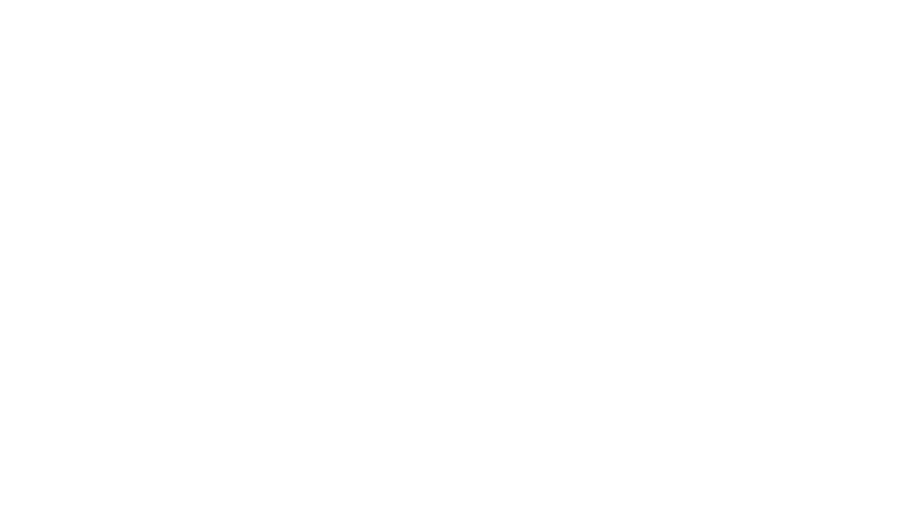
Why Zero trust is so important?
The Zero Trust framework is crucial in today’s cybersecurity landscape as it fundamentally shifts the approach to securing networks and data. Unlike traditional security models that assume trust based on location, Zero Trust operates on the principle of “never trust, always verify.” This means that every user, device, and application must be authenticated and authorized before accessing resources, regardless of whether they are inside or outside the network perimeter. By implementing this framework, organizations can better protect sensitive data from breaches, reduce the risk of insider threats, and enhance overall security posture in an increasingly complex threat environment.

Data Security
In a Zero Trust framework, data security is paramount as it operates on the principle of “never trust, always verify.” This approach emphasizes the need to protect sensitive data regardless of its location, ensuring that access is strictly controlled and continuously monitored. Key areas to focus on include implementing robust identity and access management (IAM) solutions, encrypting data both at rest and in transit, and applying micro-segmentation to limit lateral movement within the network. By prioritizing these areas, organizations can effectively safeguard their data against unauthorized access and potential breaches.
People and Identity Security
In a Zero Trust framework, People and Identity Security is essential, as it ensures that only authorized users can access sensitive resources. This approach requires a strong emphasis on identity verification through multi-factor authentication (MFA) and continuous monitoring of user behavior to detect anomalies. Additionally, organizations should prioritize user awareness and training programs to educate employees about security best practices, phishing threats, and the importance of safeguarding their credentials. Implementing strict access controls, regularly reviewing user permissions, and utilizing identity governance solutions further enhance security. By focusing on these measures, organizations can bolster their defenses against insider threats and credential misuse while fostering a security-conscious culture.
Device Security
In a Zero Trust framework, Device Security is vital, as it ensures that all endpoints accessing the network are verified and secure. This approach involves implementing stringent security measures such as endpoint detection and response (EDR), regular vulnerability assessments, and ensuring that devices comply with security policies before they can access sensitive data. Organizations should also focus on maintaining up-to-date antivirus and anti-malware solutions, enforcing encryption on devices, and utilizing mobile device management (MDM) solutions to manage and secure mobile endpoints. By prioritizing these aspects, organizations can effectively mitigate risks associated with compromised devices and ensure that only trusted endpoints can interact with their network, reinforcing overall security.
Network Security
In a Zero Trust framework, Network Security is crucial, as it protects sensitive data by enforcing strict controls over network access and communication. This approach emphasizes the principle of least privilege, ensuring that users and devices have access only to the resources necessary for their roles. Key areas of focus include implementing firewalls, intrusion detection and prevention systems (IDPS), and micro-segmentation to limit lateral movement within the network. Additionally, organizations should incorporate Network Detection and Response (NDR) solutions to provide real-time visibility into network traffic and quickly identify and respond to potential threats. Employing encrypted communication protocols and regular network traffic monitoring further enhances security. By prioritizing these strategies, organizations can strengthen their defenses against cyber threats and maintain a secure environment for data and applications
Workloads and Application security
In a Zero Trust framework, Workload and Application Security is essential to protect applications and their associated data from vulnerabilities and threats. This approach involves implementing security measures throughout the application lifecycle, including secure coding practices, regular vulnerability assessments, and automated security testing during development. Organizations should focus on container security and runtime protection to ensure that workloads are secure in cloud and on-premises environments.
Governance
and Risk
In a Zero Trust framework, Governance and Risk Management are critical for ensuring that security policies align with organizational objectives and regulatory requirements. This approach requires a comprehensive understanding of risk profiles and the implementation of policies that govern access and data usage across all systems. Organizations should focus on continuous risk assessments, ensuring that security controls are effective and up to date, and developing clear compliance protocols to address relevant regulations. Additionally, integrating security into the overall governance strategy helps in making informed decisions regarding risk tolerance and resource allocation. By prioritizing these aspects, organizations can foster a culture of accountability, enhance decision-making, and effectively manage risks in an increasingly complex threat landscape.
Visibility and Analytics
In a Zero Trust framework, Visibility and Analytics are vital for maintaining security and responding effectively to potential threats. This approach emphasizes the need for real-time monitoring and comprehensive visibility into all network activities, user behaviors, and access patterns. Organizations should invest in advanced analytics tools that leverage machine learning and artificial intelligence to identify anomalies and detect suspicious activities swiftly. By prioritizing visibility and analytics, organizations can enhance their threat detection capabilities, improve incident response times, and maintain a robust security posture that adapts to evolving risks.
Security Automation and orchestration
In a Zero Trust framework, Security Automation and Orchestration play a crucial role in streamlining security operations and enhancing response times to threats. This approach involves automating routine security tasks, such as threat detection, incident response, and vulnerability management, to reduce the burden on security teams and minimize human error. By integrating various security tools and technologies through orchestration, organizations can create a cohesive security ecosystem that allows for seamless communication and data sharing among systems. This enables faster detection and remediation of security incidents, allowing organizations to respond proactively to emerging threats. By prioritizing security automation and orchestration, organizations can enhance efficiency, improve their overall security posture, and better protect their assets in an increasingly complex threat landscape.